The Hacking Group was recently exposed by Wikileaks which published files that included confidential employee emails. In the emails, hacking group staff and Kenyan agents were in touch over a long period of time in an attempt to procure Hacking Teams software online surveillance system marketed to governments as Galileo.
There was global uproar when the emails revealed that the system was sold to Governments with a poor human rights records and could have resulted in the tracking down and arrest of activists, human rights advocates, journalists and politicians.
One such activist Ahmed Mansoor from the UAE clicked a link to open a Microsoft Word attachment. That document had a hidden file, a trojan which installed itself on his computer. Thereafter, thugs were able to track the online pro-democracy campaigner and beat him up on two different occasions.
Using well known exploits in commonly used applications such as MS Word/Excel/Pdf/ a malicious file can easily be embedded and emailed to the victim. Once a person tries to open the file, the application crashes, however the spyware will be installed and running from there on. This practice is known as spear-phishing and is one of the ways Galileo finds its way into victims phones, computers and tablets.
Another popular technique is social engineering. You may have been online and been lured to click on a link you came across shared widely on Facebook, Twitter or as a viral email. After the click, there was nothing or the page did not open however, it most likely opened and installed a small file discreetly. This file is known as the dropper which then triggers further downloads of complex spyware and connects to the command center where an operator begins surveillance.
Most of the spyware that are in use for espionage are able to gain root access to devices meaning a ‘file wipe’ will not remove the file from your hard disk, or phone. Root access also enables the the stealth spyware to avoid detection by anti virus scanners.
Read: Hacking Team expose reveals Kenyan actors
Kaspersky an antivirus company and Citizen Lab have extensively researched on Galileo’s surreptitious software. Some of the other methods that they have identified include.
- Tactical Network Injection: on LAN or WiFi (watch out for unsecured networks)
- Melted Application: bundling a Hacking Team dropper alongside a bait application (mostly on android applications)
- Local Installation: mobile installation via USB or SD card
- Silent Installer: a desktop executable that will install the implant
- Infected U3 USB: an auto-infecting USB drive
- WAP Push Message: the target will be infected if the user accepts the message (works on all mobile operating systems apart from iOS)
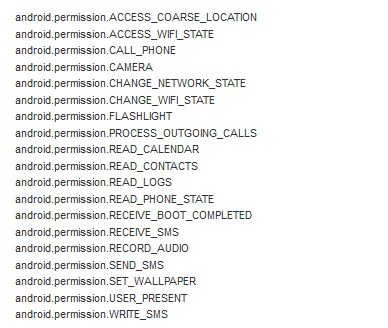
A compromised device gives up and transmits all crucial information about the targets device (citizenlab.org)
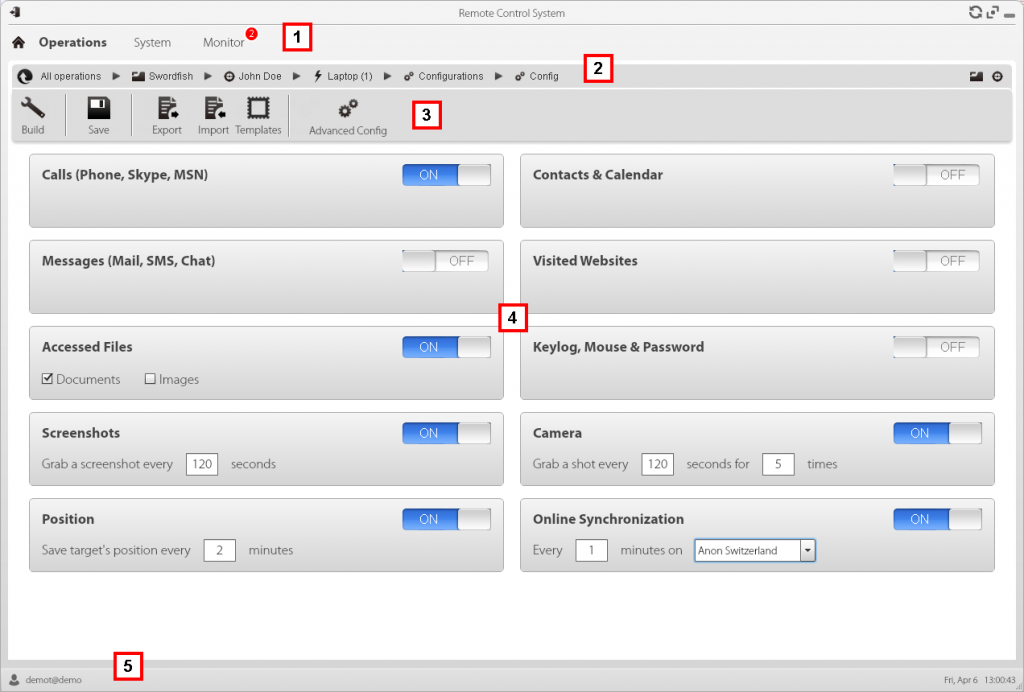
The control center gets alerted once a new device has been compromised and the operator can then see from information gathered if the target is worth pursuing. The system will have complete control over devices. The operator can switch on your webcam and microphone to see and listen to what is going on at anytime. When the Citizen Lab had a look at the the exploits, they found that the application had unlimited access to the device functions.
Once the device has been compromised, the system has tools to listen in and find out home network, or workplace wifi and subsequently install onto the the targets other devices. If successful a target will be under surveillance 24 hours a day on all devices. The system operator will synchronize with targets devices and can get minute by minute updates of screenshots, key logs (showing keyboard activity) file system, location, calendar, sim information and messages. With this information, tracking down the target is the easiest part.
No one knows for sure if the government bought the system as was discussed in the emails revealed. Whereas Galileo is primarily used for security purposes, it can be easily abused by governments seeking to suppress dissidents and activists as has been experienced elsewhere.
Is it possible that such effective surveillance tools can be abused in a system rife with corruptions such as ours?


